
Stay up to date on the latest vendor risk management news happening this month. Check out the articles below.
Recently Added Articles as of September 26
This week, headlines cover organizations' need to assess third-party information technology and cybersecurity risks, what a supply chain attack is and popular methods of it, and evaluating compliance with upcoming regulations and directives in the EU. Check out all of this week’s news below.
Addressing third-party IT risks: Mitigating third-party information technology (IT) risk has become a big priority for CISOs, particularly as supply chain incidents continue to increase. Assessing this risk typically includes reviewing software and hardware bill of materials, sending third-party questionnaires, and using publicly available data. However, each of these have their own weak points, and organizations should look to supply chain standards, like NIST, to improve their third-party risk assessments. Organizations can also take a more proactive approach by keeping a current inventory of third parties and their products, including versions, verifying codes received from the third party, and extending vulnerability and threat scanning to third parties.
Mitigating third-party cybersecurity risks: Even if an organization has an advanced cybersecurity program, they’re still exposed to third-party risks if their vendors don’t have the right cybersecurity measures in place. Smaller vendors in particular may not have the resources to invest in the best cybersecurity solutions. It's recommended that organizations vet third-party vendors, which can include external scanning and even on-site audits. However, organizations also need to look at their fourth and nth parties and evaluate those risks. Organizations should take inventory of vendors, including their products and services, use threat intelligence to understand the attack landscape, perform risk assessments to make informed decisions on vendors, and do continuous training and education on cybersecurity best practices.
Malicious Python packages target the supply chain: A North Korean hacking group is likely poisoning Python packages for developers in an attempt to attack the supply chain. The Python packages are being uploaded to the PyPl open-source repository. This repository has been a frequent target for malicious activity. In this case, the hacking group looked to target third-party vendors and gain access to their customers. Any malicious packages discovered were removed from PyPl, but organizations should still use caution when using and downloading open-source software.
Complying with third-party requirements in EU regulations and directives: The European Union (EU) has a key regulation and a key directive that emphasizes the necessity of managing third-party and supply chain risks – the Digital Operational Resilience Act (DORA) and the Network and Information Systems Directive (NIS 2). To comply, organizations should ensure they have processes in place to mitigate risks, including regular risk assessments, vulnerability scans, and security controls. It’s also critical for organizations to manage their third-party risks, which can include due diligence and questionnaires, but also requires proactive measures like threat intelligence.
Department of Justice addresses AI and other new technology in updated guidance: The Department of Justice (DOJ) released revised guidance for corporate compliance programs, addressing the use of artificial intelligence (AI) and how to address its risks. Organizations will need to consider a set of 10 questions when assessing AI risk, and these may also be helpful to ask third parties when assessing their AI risk. The questions include the organization’s approach to governance regarding technology like AI, how the organization is curbing any potential negative consequences of AI use, and are controls in place to ensure the technology is only used for its intended purposes.
What’s a supply chain attack?: Supply chain attacks seek to exploit the relationships between organizations and their third-party vendors. Some common methods seen in supply chain attacks include compromising and tampering with software with malicious code, tampering with hardware with malicious chips embedded, stealing credentials of a third-party vendor, and compromising repositories, libraries, or dependencies. By using these methods, threat actors can gain access to an organization through its third-party vendor. This is why it’s crucial for organizations to actively manage third-party risks with due diligence, continuous monitoring, limited data access, and incident response plans.
Why shippers and carriers need to invest in third-party risk management: Shippers and carriers play a critical role in the trucking and logistics industry, but as more organizations focus on supply chain risks, carriers are also coming under increased scrutiny. How carriers address their risks and cybersecurity posture can greatly impact their competitive position during the onboarding process. Carriers should map out all the connections with customers, vendors, employees, and regulators. Carriers should then assess their own third-party risks and how well those third parties are protecting your data. By investing in a third-party risk management program, carriers can be better positioned for long-term partnerships.
GitHub patches critical flaw: GitHub addressed a critical flaw that’s impacting Community Edition and Enterprise Edition. The vulnerability could allow attackers to log in as arbitrary users and compromise a vulnerable system. GitHub also urged users to enable two-factor authentication for all accounts. Organizations should also ensure they implement these latest updates and patches.
CISA added vulnerabilities to its catalog: The U.S. Cybersecurity and Infrastructure Agency (CISA) added five flaws to its Known Exploited Vulnerabilities (KEV) catalog. CISA has warned of active exploitation of some of these vulnerabilities, including one from Apache that was patched in April. Other vulnerabilities have been used in attacks in the past.
Recently Added Articles as of September 19
Summer is winding down, but the need for third-party risk management isn’t. This week’s headlines emphasized the importance of managing third-party risk in all industries, including finance, healthcare, and automotive. Read up on all the best practices and recommendations in the news below.
Preparing for third-party incidents with proactive planning: With growing third-party inventories, it’s become even more challenging to manage every third-party product or service. However, cybercriminals now have an even larger attack surface to target, increasing organizational risks. There are also other risks, like the threat of natural disaster, which can cause supply chain disruptions. It’s more important than ever to have a proactive approach to incident response and resilience. Organizations should assume that eventually an incident will impact them. Proactively developing contingency plans by identifying critical systems, data, and third parties will help organizations respond quickly. Consistent practices, like drills and simulations, will help organizations improve upon their plan by identifying any weaknesses. It’s also important to look for any overreliance on a particular third party, as this can increase the potential of a disruptive incident. Using these proactive steps can ensure your organization is better prepared.
Misconfigured ServiceNow enterprises expose sensitive data: More than 1,000 misconfigured ServiceNow enterprises exposed sensitive corporate information to external users. The information includes internal system details, user credentials, and access tokens. The exposed information came from the third-party software platform’s “Knowledge Base,” which allows organizations to share how-to guides, FAQs, and other internal procedures with employees. Organizations should ensure public access is turned off and review user criteria to ensure unauthorized users are blocked.
Google switching to ML-KEM: Google will switch from KYBER to ML-KEM in the Chrome browser to help defend against cryptographically relevant quantum computers risks. These updates will take effect in Chrome version 131, which is scheduled to be released in November.
Strengthening third-party cybersecurity practices in the automotive industry: A recent cyberattack this year on a third-party automotive software developer highlighted the importance of third-party risk management within the automotive industry. The industry relies on technology for better user experiences and more efficient vehicles. This requires the industry to use third-party vendors to offer some of the best technology, but it also opens them up to more risks. Automotive dealerships should have plans in place to identify, assess, and manage third-party risks. Following best practices, like limiting third-party data access to only what’s needed, can help mitigate the consequences of a breach. Third parties should also have contractual obligations to provide information to your organization, particularly in the case of a cyberattack.
A recap of 2024 state privacy laws: It's been another busy year for state privacy laws so far, with 7 states passing their own privacy laws. This includes Kentucky, Maryland, Minnesota, Nebraska, New Hampshire, New Jersey, and Rhode Island. These will all go into effect in 2025 and 2026. In 2025 alone, 8 state privacy laws will take effect. Other states that already had privacy laws in place also updated theirs this year. Many of these updates addressed biometric data and protections for children under 18, particularly with social media usage. It’s important for organizations to review their compliance with privacy obligations, particularly as new laws pass.
Third-party platform tightens security after summer cyberattacks: After cloud-based platform Snowflake faced cyberattacks that impacted several customers earlier this year, the third party is rolling out several security practices to tighten security. These practices include default multi-factor authentication (MFA), a 14-character password minimum, and no repeat passwords. This goes into effect for accounts created in October.
Managing risks in the healthcare industry: Healthcare organizations are an increasingly common target of data breaches, and the industry continues to face new and emerging risks. It’s important to have risk management practices in place, both internally and with third parties, and use risk assessments to identify any potential risks before they become an issue. Healthcare organizations should also keep their technology up to date and aligned with security and regulatory standards. This can help keep patient data protected both in transit and at rest. As more healthcare organizations rely on third-party vendors, they need to continuously monitor for any potential issues or risks that may arise. Healthcare organizations are responsible for ensuring third-party vendors comply with regulatory standards.
Beginning to manage third-party risks: As more third-party incidents occur, many industries and organizations are seeing the critical need for third-party risk management for the first time. Organizations should understand how their third parties could impact them and perform due diligence before the relationship begins. However, as many organizations begin to look at third-party risk, they’re dealing with vendors that have already been with the organization a long time. Experts said it’s still important to identify the risks of those third parties. It may even be helpful to put a dollar amount on the potential cost of a third-party incident to emphasize the importance of managing those risks. Many organizations may not have a choice other than to accept a third party’s risk because it’s the only organization that provides a specific product or service. That’s when each organization has to decide for itself whether it's important enough to move forward with the product or service and accept the risk.
Fortinet experiences third-party data breach: Data belonging to Fortinet was leaked on a public forum, which hackers claimed they accessed from the third-party storage site Azure SharePoint. Fortinet said it was a limited number of files accessed from the third-party storage cloud. The incident served as a reminder of securing information in third-party cloud systems and following best practices, like not sharing files publicly and using caution with storing sensitive data in the cloud.
Third-party risk management is a requirement in the financial industry: While third-party risk management isn’t a new concept in the banking industry, it’s an increasingly important one. The third-party risk landscape continues to expand and regulators are paying closer attention to banks’ third-party relationships. Practices like due diligence, contracting, ongoing monitoring, and business continuity plans are regulatory requirements in the financial industry. However, as banks face the challenge of larger third-party inventories, increased globalization, and new regulatory requirements, they can follow several key best practices. Experts recommend a clear governance structure that identifies roles and responsibilities and continuous training and awareness for employees on third-party risks.
Recently Added Articles as of September 12
Two third-party data breaches have impacted more than 2 million people, federal regulators are paying close attention to data privacy, and organizations can prepare for third-party incidents by following several best practices. Read this week’s news and headlines below.
Third-party data breach impacts almost 1 million: A third-party data breach impacted the information of more than 946,000 people at CMS. The third party, Wisconsin Physicians Service Insurance Corporation (WPS), notified of the breach in July 2024; however, it stemmed from the MOVEit breaches of 2023. At the time, WPS investigated its systems, but didn’t find evidence of exploitation. WPS didn’t discover until 2024 that a threat actor had gained access to files. Some of the information compromised included names, Social Security numbers, and Medicare beneficiary numbers.
Preparing for third-party vendor outages and incidents: The CrowdStrike outage in July reminded organizations that even large vendors can be vulnerable to issues arising. Before the next incident can occur, organizations should reevaluate who their critical third-party vendors are and their business continuity and disaster recovery plans. Testing various scenarios should include situations where a vendor’s service is no longer available. Incident response plans should also be tested alongside key vendors. Vendor risk assessments can help your organization understand the levels of vendor risks and what must be done to protect your organization.
Using collaboration to mitigate third-party cybersecurity risks: Third-party incidents can cause your organization’s operations to come to a halt. Cybercriminals have heavily targeted third-party vendors as they're often the weaker links in the supply chain. Many organizations may treat due diligence simply as a check-the-box exercise or they may not have a clear view of critical fourth-party vendors. One strategy to better mitigate third-party risks is for organizations to work together and share critical information about impending and ongoing attacks. How can organizations band together to share information on third-party vulnerabilities and work to protect that third party? This strategy may not apply in every instance, but a willingness for organization to work together could help mitigate third-party cyberattacks.
How financial institutions can protect against cyberattacks: Financial institutions have long been the target of cyberattacks and the industry is second only to healthcare for the average cost of a data breach. Financial institutions have to protect their systems while also complying with a growing regulatory landscape. It’s recommended to follow cybersecurity best practices, like regular security audits, hardware-based authentication, and advanced email filters to detect issues.
Almost 1.7 million impacted in a third-party data breach: A third-party vendor that handles payments for U.S. and Canadian organizations reported a data breach impacting almost 1.7 million people. Hackers were able to access Slim CD’s network for almost a year. Compromised data includes credit card information and physical addresses. However, the information didn’t include card verification numbers, which lessens the risk of credit card fraud. Because Slim CD is a third party, many people likely didn’t directly use the organization.
Federal regulator focuses on privacy and third-party data usage: The Federal Trade Commission (FTC) has focused more on data privacy in recent months, particularly how organizations use customer data. A recent order against Avast banned the sale or licensing of any web browsing data for advertising purposes. The order also includes two Avast subsidiaries. The FTC is considering identifiable browsing information to be sensitive data, which can include third-party cookies, webpage URLs, and image domains. In the order, the FTC said browsing data such as health concerns, location, and financial status should not be sold to third parties without first gaining consent from users. Organizations should take note of the order and review any privacy and security claims they make to users, use contractual provisions to limit third-party usage of data, and treat browsing information as sensitive data.
Malware campaign targets banking users: A new malware campaign is targeting mobile users in Brazil. It’s a banking trojan that would allow cybercriminals to use keylogging to gain access to bank information. The malware campaign is primarily through phishing attempts that trick users into installing fake dropper apps. Currently, no apps that hold the malware have been discovered in the Google Play Store, but users should still use caution when downloading applications.
Recently Added Articles as of September 5
Major Ohio city is victim of a ransomware attack: In July, the city of Columbus, Ohio experienced a ransomware attack, leading to both residents’ and non-residents’ personal information being leaked. Columbus investigated and responded to the breach quickly. Then, a local researcher reported to the media that the incident’s impact was much bigger than the city claimed. The city is suing the researcher for allegedly working with a ransomware gang to download the leaked data and spread it to cause a bigger concern.
An overview of the core use cases for artificial intelligence (AI) in third-party risk management: AI is making waves in the industry, and it can provide many benefits to organizations, especially when it comes to third-party risk management. There are three core use cases to provide value, which include assessing risks in minutes, increasing resiliency, and streamlining processes. As organizations strategically embrace AI opportunities, it can transform their business operations.
Over 400,000 breached in a radiology IT vendor hack: Specialty Networks, a Tennessee-based company providing information systems and transcription services to radiology practices, notified 411,037 people of a data breach from last December. Class-action lawsuits have been proposed and Specialty Networks will provide 12 months of identity and credit monitoring to those affected.
Are you complying with Canadian privacy laws?: Per Canada’s privacy laws, if your organization transfers personal information (PI), it’s responsible for the protection of the information. If PI is mishandled, the organization can be exposed to big risks, like noncompliance with regulatory guidelines. To comply, it’s recommended organizations thoroughly understand their vendors’ privacy and cybersecurity policies and practices, include regulatory statutes in contract terms as needed, audit vendors to verify compliance with privacy and data protections laws and contractual obligations, and ensure vendors return or destroy PI when they should no longer have access.
Ransomware-as-a-Services (RaaS) continues to be a threat: The U.S. government shared that threat actors associated with the RansomHub ransomware group encrypted and exfiltrated data from at least 210 victims since it was created in February 2024. Industries attacked include information technology, healthcare, food and agriculture, transportation, and many more. This is a good reminder to remain alert as the trend of RaaS continues.
FFIEC Cybersecurity Assessment Tool (CAT) to be sunset: The FFIEC announced the CAT will be sunset on August 31, 2025. The assessment tool was created in 2015 to assist financial institutions with identifying risks and determining cybersecurity preparedness. The FFIEC won't continue to update the CAT to reflect current government regulations and recommends institutions refer to those resources, such as the National Institute of Standards and Technology (NIST) Cybersecurity Framework 2.0 and the Cybersecurity and Infrastructure Security Agency’s (CISA) Cybersecurity Performance Goals.
Preventing cyberattacks with third-party risk management and artificial intelligence: AI can work for both good and evil. It continues to provide value to organizations across many industries, but it has also become another way scammers are successfully attacking organizations. With the introduction of generative AI tools like ChatGPT, scammers’ emails are appearing more credible. To remain vigilant, it’s recommended that organizations continue to have strong third-party risk management practices, including performing vendor due diligence, continuously monitor vendors, and creating vendor management policies. Ironically, AI can also assist with protection from attacks, as it can help with identifying attacks faster.
FFIEC issues a new booklet: An FFIEC IT Examination Handbook has been updated after 20 years! The Development, Acquisition, and Maintenance booklet gives examiners examination expectations “regarding entities’ development and acquisition planning and execution, governance and risk management, and maintenance and change management practices.” It replaces the Development and Acquisition booklet issued in April 2004.
AI vendor contract considerations: Prior to signing an AI vendor contract, it’s important to conduct due diligence on the vendor and the AI system. This includes reviewing the vendor’s reputation, prior performance, legal issues, the AI model’s architecture, and more. Also consider including contractual provisions, such as a notification requirement should there be any issues with the AI system. Other considerations to keep in mind include clear performance metrics and how intellectual property will be handled.
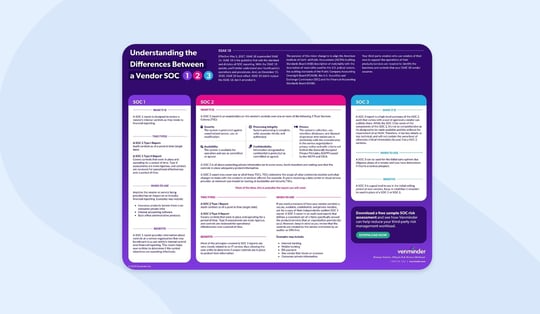
Infographic
Learn the differences between a vendor SOC 1, 2, and 3 in this infographic.
Related Posts
FFIEC Development, Acquisition, Maintenance Booklet TPRM Highlights
The Federal Financial Institutions Examination Council’s (FFIEC) Development and Acquisition...
Top 5 Reasons to Be Thankful for Third-Party Risk Management
Third-party risk management is a comprehensive concept and can be very demanding at times. We fully...
FDIC Highlights Third-Party Oversight Failures in Supervisory Report
Each year, the Federal Deposit Insurance Corporation (FDIC) performs a series of regulatory...
Subscribe to Venminder
Get expert insights straight to your inbox.
Ready to Get Started?
Schedule a personalized solution demonstration to see if Venminder is a fit for you.
